simpleSAMLphp on IIS from scratch (with AD FS)
IIS Configuration for simpleSAMLphp
IIS Configuration for simpleSAMLphp
As per the requirements section, I will be using a domain account that is set also as local Administrator for the server I’m using.
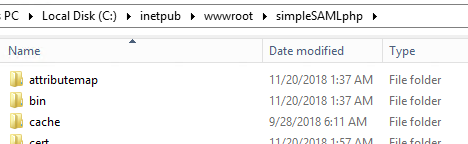
- If you haven’t done it yet, download simpleSAMLphp’s compressed files (see the requirements section for the link) and extract the content wherever the physical path for this simpleSAMLphp application will be. In our case, we’ll call the application simpleSAMLphp and we’ll extract all files under C:\inetput\wwwroot\simpleSAMLphp.
- As the application pool will run with a local admin account, you won’t need to set any NTFS permission if you’re using the default permissions (that automatically allow the local Administrators group). If you want to use the default app pool with IUSR, make sure you allow IUSR to modify C:\inetput\wwwroot\simpleSAMLphp\log (if you’re going to use local logs, we’ll see this later on).
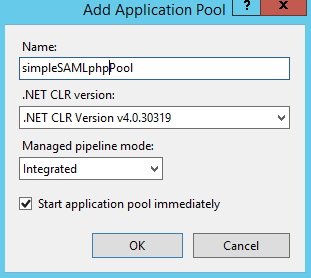
- Open IIS Manager, expand the server name on the left, right click on Application Pools and click on Add Application Pool.
- Give it a name and click Ok.
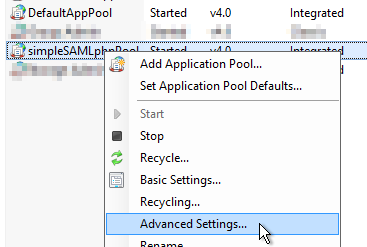
- Right click on the newly created pool and click Advanced Settings.
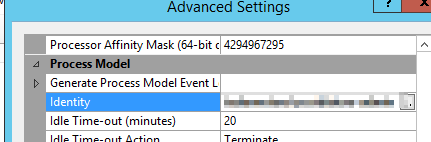
- Scroll under Process Model > Identity and change it to use the service account you want, in my case it’s going to be a domain account.
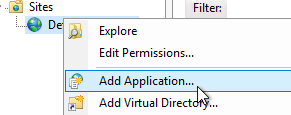
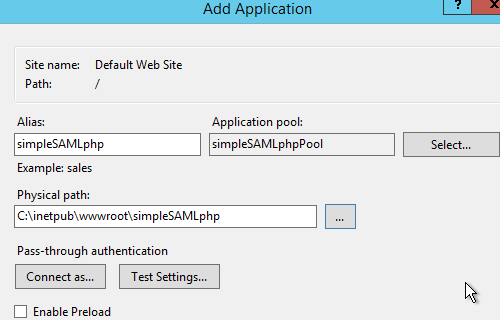
- Right click on Default Web Site and click Add Application.
- Name the application, select the application pool created above and finally point it to where we extracted all simpleSAMLphp’s files.
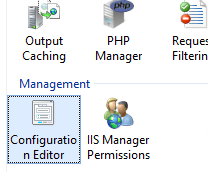
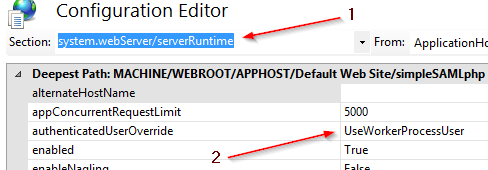
- As I want my web application to actually run with the service account specified, we need to change a little configuration in IIS’s Configuration Editor. Click on simpleSAMLphp’s web application, under Default Web Site and double click on Configuration Editor.
- Under Section, select system.webServer/serverRuntime and under authenticatedUsersOverride set it to UseWorkerProcessUser.
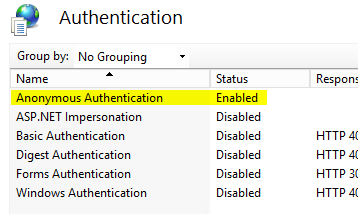
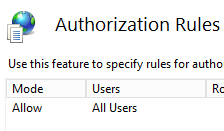
- Now, we want to set this up so that anybody can reach this web site, you can look at restricting this later on, but for now, let’s configure it to enable Anonymous Authentication (Windows’ to disabled) and make sure all users can access it.